1 Advisory and 1 Update Published – 12-30-25
Today CISA’s NCCIC-ICS published a control system security advisory for products from WHILL. They also updated an advisory for products from AzeoTech.
WHILL Advisory
This advisory describes a missing authentication for critical function vulnerability in the WHILL Model C2 Electric Wheelchairs and Model F Power Chairs. The vulnerability was reported to CISA by Billy Rios, Jesse Young, Brandon Rothel, Jonathan Butts, Henri Hein, Justin Boling, Nick Kulesza, Ken Natividad, and Carl Schuettthe of the Exploit Development Team - QED Secure Solutions. WHILL has ‘deployed fixes’ for the vulnerability.
NCCIC-ICS reports that successful exploitation of this vulnerability could allow an attacker within Bluetooth range to take control over the product.
AzeoTech Update
This update provides additional information on the DAQFactory advisory that was originally published on December 11th, 2025. CISA does not provide any information on the changes being made. A quick check shows that two of the vulnerabilities have been removed from the advisory. They also added researcher names for the vulnerabilities reported through the Zero Day Initiative.
DTR Missing Vulnerabilities
Two vulnerabilities that were in the original AzeoTech advisory were removed from today’s updated advisory. They were:
Stack-based buffer overflow - CVE-2025-66584, and
Heap-based buffer overflow - CVE-2025-66587.
Both of these vulnerabilities are now listed at NVD.NIST.gov as ‘REJECTED’ with the following explanation: “This CVE ID has been rejected or withdrawn by its CVE Numbering Authority.” Typically this should mean that the vendor found a reason to object to the described vulnerability that was accepted by CISA.
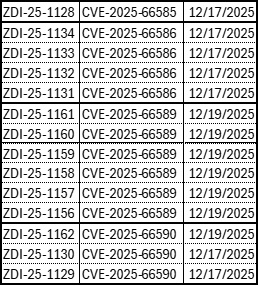
According to the original advisory both vulnerabilities were reported by ZDI. Neither of those CVE numbers is listed in the current online ZDI vulnerability spreadsheet. Interestingly, ZDI reports 14 separate AzeoTech vulnerabilities using four of the five CVE’s listed in today’s updated advisory (See the table listed below). Those advisories were published on December 17th and 19th, so they were not available when I posted about the original CISA advisory on December 12th, 2025.
As I have noted here before, this is not an unusual occurrence with ZDI advisories. It has appeared that ZDI reports variations on a theme vulnerabilities that CISA has combined in to single vulnerabilities. I am not so sure that is the case here. Lets look at the three vulnerabilities reported under CVE-2025-66590, the bottom three in the table:
ZDI-25-1129 - Out-Of-Bounds Write Remote Code Execution Vulnerability - Rocco Calvi,
ZDI-25-1130 - Out-Of-Bounds Write Remote Code Execution Vulnerability- Andrea Micalizzi, and
ZDI-25-1162 - Memory Corruption Remote Code Execution Vulnerability - Rocco Calvi
It looks like the first two could have been the same vulnerability being reported by different researchers. In fact Calvi reported #1129 on September 11th, 2025, while Micalizzi reported #1130 on June 23rd, 2025. The description of the vulnerability process is also slightly different in the two advisories. The #1129 advisory notes that the flaw “can result in a write past the end of an allocated object” where the #1130 notes that the flaw “can result in a write past the end of an allocated buffer”. It is not clear if that is just an editorial word choice difference or whether it is the description of separate vulnerabilities. The #1162 advisory clearly describes a memory corruption issue not a buffer overflow. There is no indication why it was included as a CVE-2025-66590 vulnerability.